User Manual
Table Of Contents
- Contents
- Figures
- Preface
- Section I
- Basic Operations
- Chapter 1
- Starting a Web Browser Management Session
- Chapter 2
- Basic Switch Parameters
- Chapter 3
- Enhanced Stacking
- Chapter 4
- SNMPv1 and SNMPv2c Community Strings
- Chapter 5
- Port Parameters
- Chapter 6
- MAC Address Table
- Chapter 7
- Static Port Trunks
- Chapter 8
- Port Mirroring
- Section II
- Advanced Operations
- Chapter 9
- File System
- Chapter 10
- File Downloads and Uploads
- Chapter 11
- Event Log and Syslog Servers
- Chapter 12
- Classifiers
- Chapter 13
- Access Control Lists
- Chapter 14
- Quality of Service
- Chapter 15
- Class of Service
- Chapter 16
- IGMP Snooping
- Chapter 17
- Denial of Service Defense
- Chapter 18
- Power Over Ethernet
- Section III
- SNMPv3 Operations
- Chapter 19
- SNMPv3
- Enabling the SNMP Protocol
- Configuring the SNMPv3 User Table
- Configuring the SNMPv3 View Table
- Configuring the SNMPv3 Access Table
- Configuring the SNMPv3 SecurityToGroup Table
- Configuring the SNMPv3 Notify Table
- Configuring the SNMPv3 Target Address Table
- Configuring the SNMPv3 Target Parameters Table
- Configuring the SNMPv3 Community Table
- Displaying SNMPv3 Tables
- Section IV
- Spanning Tree Protocols
- Chapter 20
- Spanning Tree, Rapid Spanning Tree, and Multiple Spanning Tree Protocols
- Section V
- Virtual LANs
- Chapter 21
- Port-based and Tagged Virtual LANs
- Chapter 22
- GARP VLAN Registration Protocol
- Chapter 23
- Protected Ports VLANs
- Section VI
- Port Security
- Chapter 24
- MAC Address-based Port Security
- Chapter 25
- 802.1x Port-based Network Access Control
- Section VII
- Management Security
- Chapter 26
- Encryption Keys, PKI, and SSL
- Chapter 27
- Secure Shell Protocol
- Chapter 28
- TACACS+ and RADIUS Authentication Protocols
- Chapter 29
- Management Access Control List
- Index
AT-S62 Management Software Web Browser Interface User’s Guide
Section VII: Management Security 347
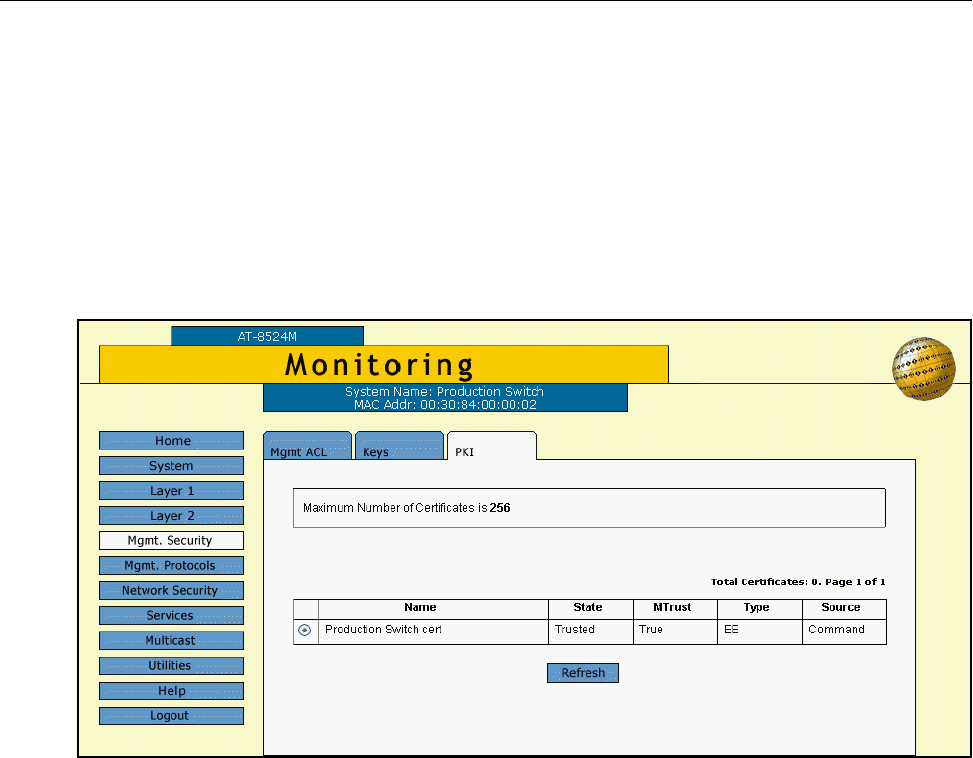
Displaying PKI Settings and Certificates
To display the self-signed and CA certificates stored in the certificate
database and the PKI settings, do the following:
1. From the Home page, select Monitoring.
2. Select the Mgmt. Security menu selection.
3. Select the PKI tab.
The PKI tab is shown in Figure 112.
Figure 113. PKI Tab (Monitoring)
The upper section states the maximum number of certificates that can
be configured on the switch.
The lower section displays a table that lists the currently configured
certificates and contains the following columns of information:
Name
The certificate name.
State
The state of the certificate, one of the following:
Trusted - The certificate is from a trusted CA.
Untrusted - The certificate is from an untrusted CA.










