Concept Guide
Table Of Contents
- About this Guide
- About Instant
- Setting up a W-IAP
- Automatic Retrieval of Configuration
- Instant User Interface
- Initial Configuration Tasks
- Customizing W-IAP Settings
- Modifying the W-IAP Host Name
- Configuring Zone Settings on a W-IAP
- Specifying a Method for Obtaining IP Address
- Configuring External Antenna
- Configuring Radio Profiles for a W-IAP
- Configuring Uplink VLAN for a W-IAP
- Changing the W-IAP Installation Mode
- Changing USB Port Status
- Master Election and Virtual Controller
- Adding a W-IAP to the Network
- Removing a W-IAP from the Network
- VLAN Configuration
- IPv6 Support
- Wireless Network Profiles
- Configuring Wireless Network Profiles
- Configuring Fast Roaming for Wireless Clients
- Configuring Modulation Rates on a WLAN SSID
- Multi-User-MIMO
- Management Frame Protection
- Disabling Short Preamble for Wireless Client
- Editing Status of a WLAN SSID Profile
- Editing a WLAN SSID Profile
- Deleting a WLAN SSID Profile
- Wired Profiles
- Captive Portal for Guest Access
- Understanding Captive Portal
- Configuring a WLAN SSID for Guest Access
- Configuring Wired Profile for Guest Access
- Configuring Internal Captive Portal for Guest Network
- Configuring External Captive Portal for a Guest Network
- Configuring Facebook Login
- Configuring Guest Logon Role and Access Rules for Guest Users
- Configuring Captive Portal Roles for an SSID
- Configuring Walled Garden Access
- Authentication and User Management
- Managing W-IAP Users
- Supported Authentication Methods
- Supported EAP Authentication Frameworks
- Configuring Authentication Servers
- Understanding Encryption Types
- Configuring Authentication Survivability
- Configuring 802.1X Authentication for a Network Profile
- Enabling 802.1X Supplicant Support
- Configuring MAC Authentication for a Network Profile
- Configuring MAC Authentication with 802.1X Authentication
- Configuring MAC Authentication with Captive Portal Authentication
- Configuring WISPr Authentication
- Blacklisting Clients
- Uploading Certificates
- Roles and Policies
- DHCP Configuration
- Configuring Time-Based Services
- Dynamic DNS Registration
- VPN Configuration
- IAP-VPN Deployment
- Adaptive Radio Management
- Deep Packet Inspection and Application Visibility
- Voice and Video
- Services
- Configuring AirGroup
- Configuring a W-IAP for RTLS Support
- Configuring a W-IAP for Analytics and Location Engine Support
- Managing BLE Beacons
- Clarity Live
- Configuring OpenDNS Credentials
- Integrating a W-IAP with Palo Alto Networks Firewall
- Integrating a W-IAP with an XML API Interface
- CALEA Integration and Lawful Intercept Compliance
- Cluster Security
- W-IAP Management and Monitoring
- Uplink Configuration
- Intrusion Detection
- Mesh W-IAP Configuration
- Mobility and Client Management
- Spectrum Monitor
- W-IAP Maintenance
- Monitoring Devices and Logs
- Hotspot Profiles
- ClearPass Guest Setup
- IAP-VPN Deployment Scenarios
- Acronyms and Abbreviations
308 | W-IAP Management and Monitoring Dell Networking W-Series Instant 6.5.1.0-4.3.1.0 | User Guide
In the W-AirWave User Interface (UI), you can select either Manage Read/Write or Monitor-only+Firmware
Upgrades as management modes. When the W-AirWave Management level is set to Manage Read/Write,
the Instant UI is in read-only mode. When the W-AirWave Management level is set to Monitor-
only+Firmware Upgrades, the Instant UI changes to the read-write mode.
With the latest version of W-AirWave, a new option in the AMP is available to put the W-IAP in config-only
mode. In this mode, the W-IAP will receive the firmware upgrades and configurations, but will not send any
statistics for monitoring. The load is reduced on W-IAP and W-AirWave and this assists in scaling W-AirWave
effectively.
Template-Based Configuration
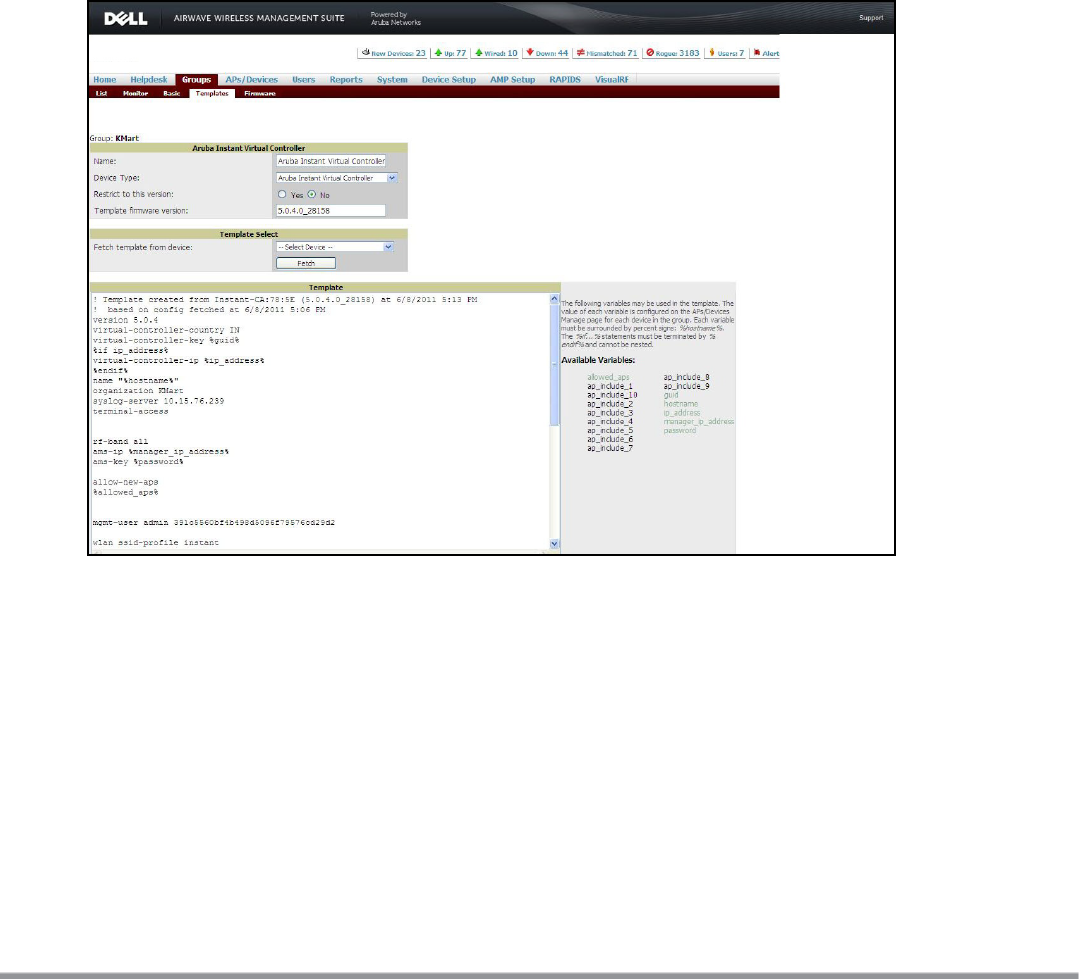
W-AirWave automatically creates a configuration template based on any of the existing W-IAPs, and it applies
that template across the network as shown in the following figure. It audits every device on an ongoing basis to
ensure that configurations never vary from the enterprise policies. It alerts you whenever a violation is
detected and automatically repairs the incorrectly configured devices.
Figure 82 Template-Based Configuration
Trending Reports
W-AirWave saves up to 14 months of actionable information, including network performance data and user
roaming patterns, so you can analyze how network usage and performance trends have changed over time. It
also provides detailed capacity reports with which you can plan the capacity and appropriate strategies for
your organization.
Intrusion Detection System (IDS)
W-AirWave provides advanced, rules-based rogue classification. It automatically detects rogue W-IAPs
irrespective of their location in the network and prevents authorized W-IAPs from being detected as rogue W-
IAPs. It tracks and correlates the IDS events to provide a complete picture of network security.










