Concept Guide
Table Of Contents
- About this Guide
- About Instant
- Setting up a W-IAP
- Automatic Retrieval of Configuration
- Instant User Interface
- Initial Configuration Tasks
- Customizing W-IAP Settings
- Modifying the W-IAP Host Name
- Configuring Zone Settings on a W-IAP
- Specifying a Method for Obtaining IP Address
- Configuring External Antenna
- Configuring Radio Profiles for a W-IAP
- Configuring Uplink VLAN for a W-IAP
- Changing the W-IAP Installation Mode
- Changing USB Port Status
- Master Election and Virtual Controller
- Adding a W-IAP to the Network
- Removing a W-IAP from the Network
- VLAN Configuration
- IPv6 Support
- Wireless Network Profiles
- Configuring Wireless Network Profiles
- Configuring Fast Roaming for Wireless Clients
- Configuring Modulation Rates on a WLAN SSID
- Multi-User-MIMO
- Management Frame Protection
- Disabling Short Preamble for Wireless Client
- Editing Status of a WLAN SSID Profile
- Editing a WLAN SSID Profile
- Deleting a WLAN SSID Profile
- Wired Profiles
- Captive Portal for Guest Access
- Understanding Captive Portal
- Configuring a WLAN SSID for Guest Access
- Configuring Wired Profile for Guest Access
- Configuring Internal Captive Portal for Guest Network
- Configuring External Captive Portal for a Guest Network
- Configuring Facebook Login
- Configuring Guest Logon Role and Access Rules for Guest Users
- Configuring Captive Portal Roles for an SSID
- Configuring Walled Garden Access
- Authentication and User Management
- Managing W-IAP Users
- Supported Authentication Methods
- Supported EAP Authentication Frameworks
- Configuring Authentication Servers
- Understanding Encryption Types
- Configuring Authentication Survivability
- Configuring 802.1X Authentication for a Network Profile
- Enabling 802.1X Supplicant Support
- Configuring MAC Authentication for a Network Profile
- Configuring MAC Authentication with 802.1X Authentication
- Configuring MAC Authentication with Captive Portal Authentication
- Configuring WISPr Authentication
- Blacklisting Clients
- Uploading Certificates
- Roles and Policies
- DHCP Configuration
- Configuring Time-Based Services
- Dynamic DNS Registration
- VPN Configuration
- IAP-VPN Deployment
- Adaptive Radio Management
- Deep Packet Inspection and Application Visibility
- Voice and Video
- Services
- Configuring AirGroup
- Configuring a W-IAP for RTLS Support
- Configuring a W-IAP for Analytics and Location Engine Support
- Managing BLE Beacons
- Clarity Live
- Configuring OpenDNS Credentials
- Integrating a W-IAP with Palo Alto Networks Firewall
- Integrating a W-IAP with an XML API Interface
- CALEA Integration and Lawful Intercept Compliance
- Cluster Security
- W-IAP Management and Monitoring
- Uplink Configuration
- Intrusion Detection
- Mesh W-IAP Configuration
- Mobility and Client Management
- Spectrum Monitor
- W-IAP Maintenance
- Monitoring Devices and Logs
- Hotspot Profiles
- ClearPass Guest Setup
- IAP-VPN Deployment Scenarios
- Acronyms and Abbreviations
376 | Hotspot Profiles Dell Networking W-Series Instant 6.5.1.0-4.3.1.0 | User Guide
You can specify any of the following EAP methods for the nai-realm-eap-method <eap-method> command:
l identity—To use EAP Identity type. The associated numeric value is 1.
l notification—To allow the hotspot realm to use EAP Notification messages for authentication. The
associated numeric value is 2.
l one-time-password—To use Authentication with a single-use password. The associated numeric value is 5.
l generic-token-card—To use EAP Generic Token Card (EAP-GTC). The associated numeric value is 6.
l eap-tls—To use EAP-Transport Layer Security. The associated numeric value is 13.
l eap-sim—To use EAP for Global System for Mobile Communication (GSM) Subscriber Identity Modules
(SIM). The associated numeric value is 18.
l eap-ttls—To use EAP-Tunneled Transport Layer Security. The associated numeric value is 21.
l peap—To use protected Extensible Authentication Protocol. The associated numeric value is 25.
l crypto-card—To use crypto card authentication. The associated numeric value is 28.
l peapmschapv2—To use PEAP with Microsoft Challenge Handshake Authentication Protocol version 2
(MSCHAPv2). The associated numeric value is 29.
l eap-aka—To use EAP for Universal Mobile Telecommunications System (UMTS) Authentication and Key
Agreement (AKA). The associated numeric value is 50.
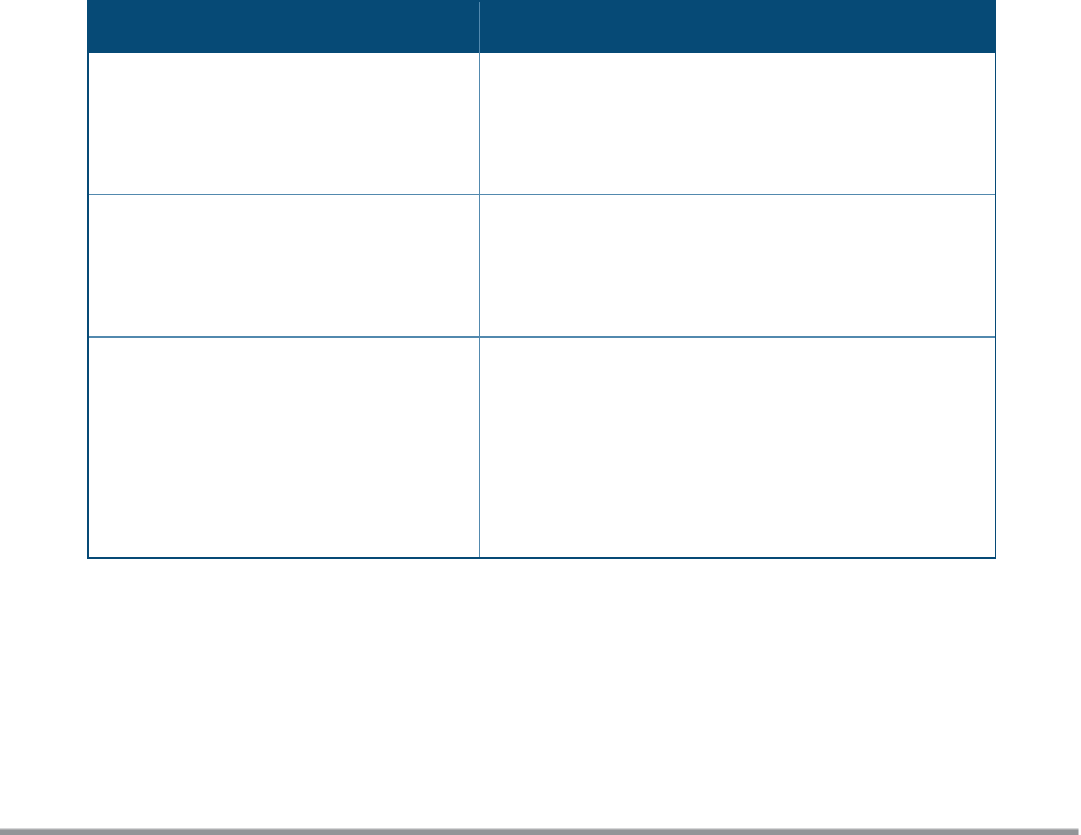
The following table lists the possible authentication IDs and their respective values:
Authentication ID
Authentication Value
reserved
l Uses the reserved authentication
method.
l The associated numeric value is 0.
—
expanded-eap
l Uses the expanded EAP authentication
method.
l The associated numeric value is 1.
Use expanded-eap as the authentication value.
non-eap-inner-auth
l Uses non-EAP inner authentication type.
l The associated numeric value is 2.
The following authentication values apply:
l reserved—The associated numeric value is 0.
l pap—The associated numeric value is 1.
l chap—The associated numeric value is 2.
l mschap—The associated numeric value is 3.
l mschapv2—The associated numeric value is 4.
Table 79: NAI Realm Profile Configuration Parameters










