HP Integrity iLO 2 Operations Guide
Table Of Contents
- HP Integrity iLO 2 Operations Guide
- Contents
- About This Document
- 1 Introduction to iLO 2
- Features
- Standard Features
- Always-On Capability
- Virtual Front Panel
- Multiple Access Methods
- Security
- User Access Control
- Multiple Users
- IPMI over LAN
- System Management Homepage
- Firmware Upgrades
- Internal Subsystem Information
- DHCP and DNS Support
- Group Actions
- Group Actions Using HP SIM
- SNMP
- SMASH
- SM CLP
- Mirrored Console
- Remote Power Control
- Power Regulation
- Event Logging
- Advanced Features
- Standard Features
- Obtaining and Activating iLO 2 Advanced Pack Licensing
- Supported Systems and Required Components and Cables
- Integrity iLO 2 Supported Browsers and Client Operating Systems
- Security
- Features
- 2 Ports and LEDs
- 3 Getting Connected to iLO 2
- 4 Logging In to iLO 2
- 5 Adding Advanced Features
- Lights-Out Advanced KVM Card for sx2000 Servers
- Lights-Out Advanced KVM card Requirements
- Configuring the Lights-Out Advanced KVM Card
- Lights-Out Advanced KVM Card IRC Feature
- Lights-Out Advanced KVM Card vMedia Feature
- Installing the Lights-Out Advanced KVM Card in a Server
- Lights-Out Advanced KVM Card Quick Setup Steps
- Using Lights-Out Advanced KVM Features
- Mid Range PCI Backplane Power Behavior
- Troubleshooting the Lights-Out Advanced KVM Card
- Core I/O Card Configurations
- Supported PCI-X Slots
- Upgrading the Lights-Out Advanced KVM Card Firmware
- Lights-Out Advanced KVM Card for sx2000 Servers
- 6 Accessing the Host (Operating System) Console
- 7 Configuring DHCP, DNS, LDAP, and Schema-Free LDAP
- 8 Using iLO 2
- Text User Interface
- MP Command Interfaces
- MP Main Menu
- MP Main Menu Commands
- CO (Console): Leave the MP Main Menu and enter console mode
- VFP (Virtual Front Panel): Simulate the display panel
- CM (Command Mode): Enter command mode
- SMCLP (Server Management Command Line Protocol): Switch to the SMASH SMCLP
- CL (Console Log): View the history of the console output
- SL (Show Logs): View events in the log history
- HE (Help): Display help for the menu or command in the MP Main Menu
- X (Exit): Exit iLO 2
- MP Main Menu Commands
- Command Menu
- Command Line Interface Scripting
- Command Menu Commands and Standard Command Line Scripting Syntax
- BP: Reset BMC passwords
- BLADE: Display BLADE parameters
- CA: Configure asynchronous local serial port
- DATE: Display date
- DC (Default Configuration): Reset all parameters to default configurations
- DF: Display FRU information
- DI: Disconnect LAN, WEB, SSH, or Console
- DNS: DNS settings
- FW: Upgrade the MP firmware
- HE: Display help for menu or command in command menu interface
- ID: System information settings
- IT: Inactivity timeout settings
- LC: LAN configuration usage
- LDAP: LDAP directory settings
- LM: License management
- LOC: Locator UID LED configuration
- LS: LAN status
- PC: Power control access
- PM: Power regulator mode
- PR: Power restore policy configuration
- PS: Power status
- RB: Reset BMC
- RS: Reset system through the RST signal
- SA: Set access LAN/WEB/SSH/IPMI over LAN ports
- SNMP: Configure SNMP parameters
- SO: Security option help
- SS: System Status
- SYSREV: Firmware revisions
- TC: System reset through INIT or TOC signal
- TE: Send a message to other mirroring terminals
- UC: User Configuration (users, passwords, and so on)
- WHO: Display a list of iLO 2 connected users
- XD: iLO 2 Diagnostics or reset
- Web GUI
- System Status
- Remote Serial Console
- Integrated Remote Console
- Virtual Media
- Power Management
- Administration
- BL c-Class
- Help
- SMASH Server Management Command Line Protocol
- SM CLP Features and Functionality Overview
- Accessing the SM CLP Interface
- Using the SM CLP Interface
- SM CLP Syntax
- System1 Target
- System Reset Power Status and Power Control
- Map1 (iLO 2) Target
- Text Console Services
- Firmware Revision Display and Upgrade
- Remote Access Configuration
- Network Configuration
- User Accounts Configuration
- LDAP Configuration
- Text User Interface
- 9 Installing and Configuring Directory Services
- Directory Services
- Directory Services for Active Directory
- Directory Services for eDirectory
- Installing and Initializing Snap-In for eDirectory
- Example: Creating and Configuring Directory Objects for Use with iLO 2 Devices in eDirectory
- Directory Services Objects for eDirectory
- Setting Role Restrictions
- Setting Time Restrictions
- Setting Lights-Out Management Device Rights
- Installing Snap-Ins and Extending Schema for eDirectory on a Linux Platform
- Using the LDAP Command to Configure Directory Settings in iLO 2
- User Login Using Directory Services
- Certificate Services
- Directory-Enabled Remote Management
- Directory Services Schema (LDAP)
- Glossary
- Index
These restrictions include the following:
• Time Restrictions
• IP Network Address Restrictions
IP/Mask◦
◦ IP Range
• DNS Name
Setting Time Restrictions
You can manage the hours available for login by members of a role using the time grid displayed
in the Role Restrictions subtab (Figure 64). You can select the times available for login for each
day of the week in half-hour increments. You can change a single square by clicking it or change
a section of squares by clicking and holding the mouse button, dragging the cursor across the
squares to be changed, and releasing the mouse button. The default setting is to allow access at
all times.
Defining Client IP Address or DNS Name Access
You can grant or deny access to an IP address, IP address range, or DNS names.
Using the By Default list, select whether to allow or deny access from all addresses except the
specified IP addresses, IP address ranges, and DNS names.
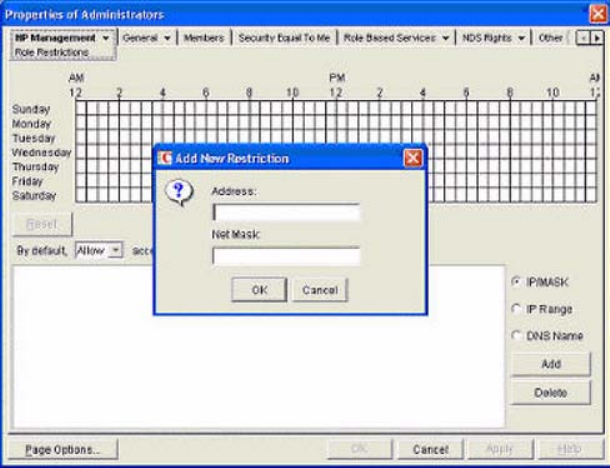
1. To restrict an IP address, select IP/MASK in the Role Restrictions subtab and click Add. The
Add New Restriction dialog box for the IP/Mask option appears.
2. In the Add New Restriction dialog box (Figure 65), enter the information, and click OK.
Figure 65 Add New Restriction Dialog Box
3. In the Role Restrictions subtab, select DNS Name and click Add. The DNS Name option enables
you to restrict access based on a single DNS name or a subdomain, entered in the form of
host.company.com or *.domain.company.com. The New DNS Name Restriction dialog box
appears.
4. Enter the information and click OK.
5. To save the changes, click Apply.
To remove any of the entries, highlight the entry in the display field and click Delete.
190 Installing and Configuring Directory Services










