Quick Reference Guide
Table Of Contents
- Reference Manual for the Model DG834 ADSL Firewall Router
- Contents
- Chapter 1 About This Guide
- Chapter 2 Introduction
- Chapter 3 Connecting the Router to the Internet
- What You Need Before You Begin
- Connecting the DG834 to Your LAN
- Auto-Detecting Your Internet Connection Type
- Testing Your Internet Connection
- Manually Configuring Your Internet Connection
- Chapter 4 Protecting Your Network
- Chapter 5 Managing Your Network
- Chapter 6 Advanced Configuration
- Chapter 7 Troubleshooting
- Appendix A Technical Specifications
- Appendix B Network and Routing Basics
- Appendix C Preparing Your Network
- Preparing Your Computers for TCP/IP Networking
- Configuring Windows 95, 98, and Me for TCP/IP Networking
- Configuring Windows NT4, 2000 or XP for IP Networking
- DHCP Configuration of TCP/IP in Windows XP, 2000, or NT4
- Configuring the Macintosh for TCP/IP Networking
- Verifying the Readiness of Your Internet Account
- Restarting the Network
- Glossary
Reference Manual for the Model DG834 ADSL Firewall Router
Managing Your Network 5-11
Log entries are described in Table 5-1 below:
Log action buttons are described in Table 5-2
Selecting What Information to Log
Besides the standard information listed above, you can choose to log additional information. Those
optional selections are as follows:
• Attempted access to blocked site
• Connections to the Web-based interface of the router
• Router operation (start up, get time, etc.)
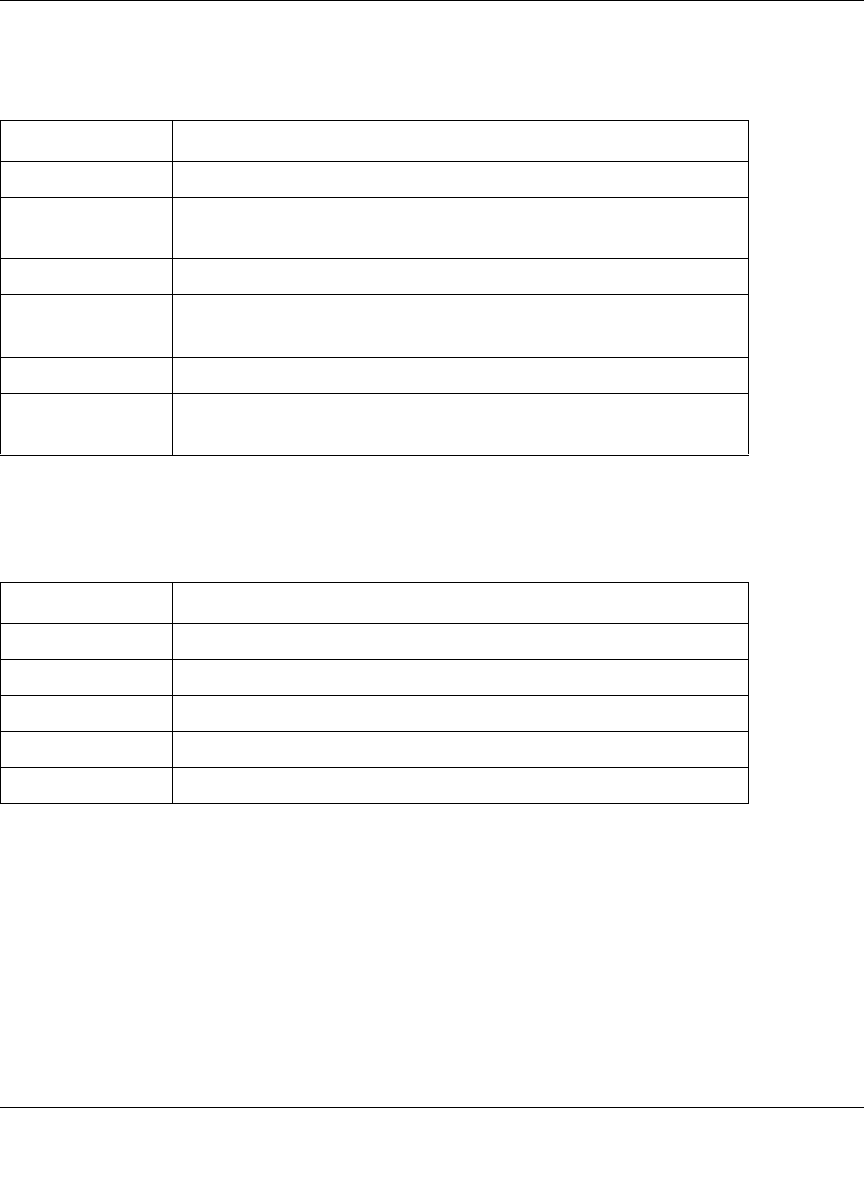
Table 5-1. Security Log entry descriptions
Field Description
Date and Time The date and time the log entry was recorded.
Description or
Action
The type of event and what action was taken if any.
Source IP The IP address of the initiating device for this log entry.
Source port and
interface
The service port number of the initiating device, and whether it
originated from the LAN or WAN
Destination The name or IP address of the destination device or Web site.
Destination port
and interface
The service port number of the destination device, and whether
it’s on the LAN or WAN.
Table 5-2. Security Log action buttons
Field Description
Refresh Refresh the log screen.
Clear Log Clear the log entries.
Send Log Email the log immediately.
Apply Apply the current settings.
Cancel Clear the current settings.










