User Manual
Table Of Contents
- 24-Port Gigabit Smart Managed Pro Switch with PoE+ and 2 SFP Ports Model GS724TPv2
- Contents
- 1. Get Started
- Switch Management Interface Overview
- Change the Default IP Address of the Switch
- Discover a Switch in a Network With a DHCP Server
- Discover a Switch in a Network Without a DHCP Server
- Configure the Network Settings on Your Computer
- Access the Web Browser–Based Management Interface
- About the User Interfaces
- Use a Web Browser to Access the Switch and Log In
- Web Browser–Based Management Interface Device View
- Interface Naming Conventions
- Configure Interface Settings
- Context-Sensitive Help and Access to the Support WebSite
- Register Your Product
- 2. Configure System Information
- 3. Configure Switching
- Configure Port Settings
- Configure Link Aggregation Groups
- Configure VLANs
- Configure a Voice VLAN
- Configure Auto-VoIP
- Configure Spanning Tree Protocol
- Configure Multicast
- View the MFDB Table
- View the MFDB Statistics
- IGMP Snooping Overview
- Configure IGMP Snooping
- Configure IGMP Snooping for Interfaces
- View the IGMP Snooping Table
- Configure IGMP Snooping for VLANs
- Modify IGMP Snooping Settings for a VLAN
- IGMP Snooping Querier Overview
- Configure IGMP Snooping Querier
- Configure IGMP Snooping Querier for VLANs
- Display IGMP Snooping Querier for VLAN Status
- Configure a Static Multicast Group
- Remove a Static Multicast Group
- Configure Multicast Group Membership
- Configure the Multicast Forward All Option
- View and Configure the MAC Address Table
- 4. Configure Quality of Service
- 5. Manage Device Security
- Configure the Management Security Settings
- Configure Management Access
- Configure Port Authentication
- Configure Traffic Control
- Configure Access Control Lists
- Use the ACL Wizard to Create a Simple ACL
- Configure a MAC ACL
- Configure MAC ACL Rules
- Configure MAC Bindings
- View or Delete MAC ACL Bindings in the MAC Binding Table
- Configure an IP ACL
- Configure Rules for a Basic IP ACL
- Configure Rules for an Extended IP ACL
- Configure IP ACL Interface Bindings
- View or Delete IP ACL Bindings in the IP ACL Binding Table
- 6. Monitor the System
- 7. Maintenance
- A. Configuration Examples
- B. Specifications and Default Settings
Manage Device Security
192
NETGEAR 24-Port Gigabit Smart Managed Pro Switch with PoE+ and 2 SFP Ports Model GS724TPv2
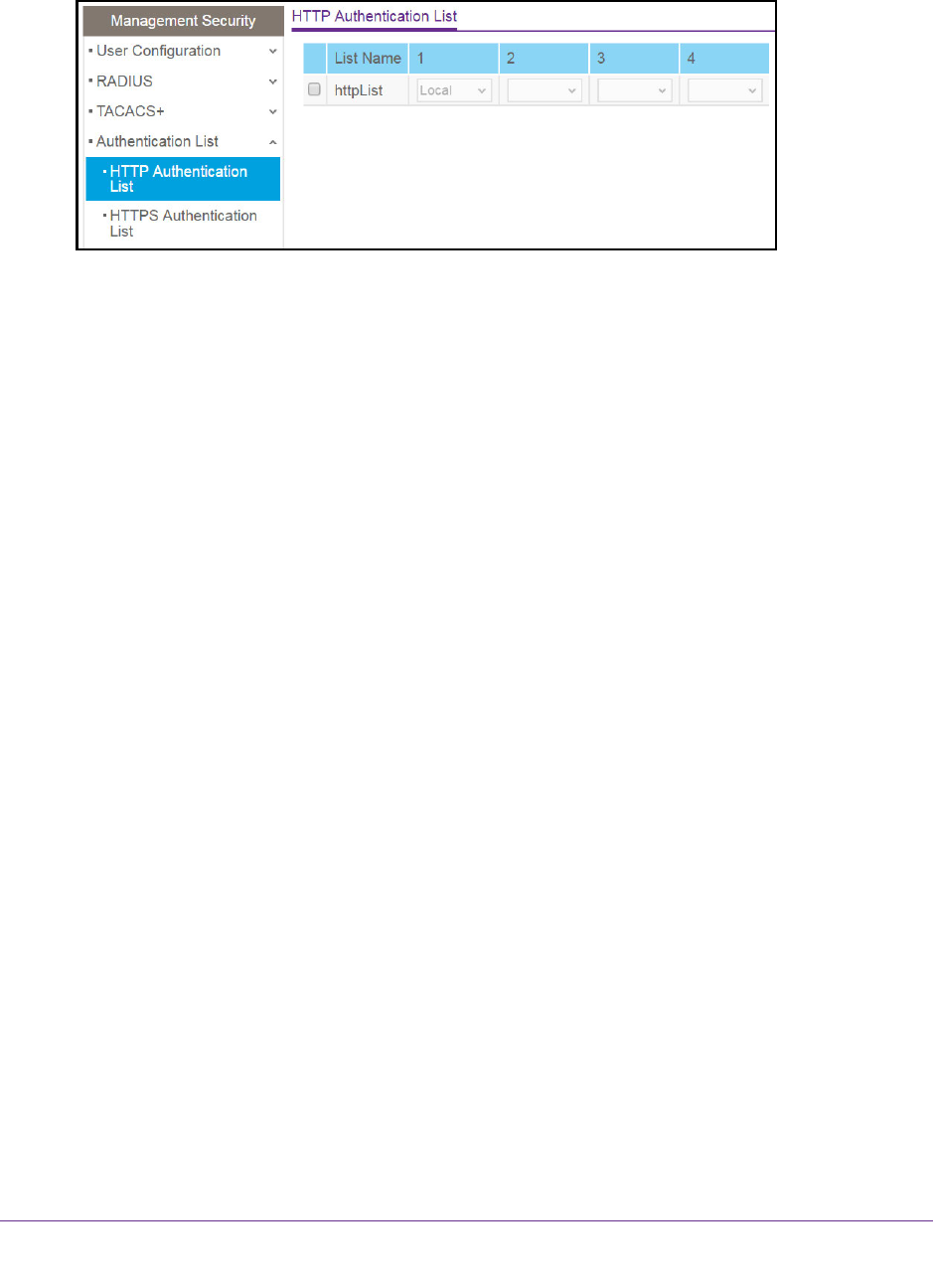
5. Select Security > Management Security > Authentication List > HTTP Authentication
List.
6. Select the check box next to the httpList name.
7. From the menu in the 1 column, select the authentication method that must be used first in
the selected authentication login list.
If you select a method that does not time out as the first method, such as Local, no other
method is tried, even if you specified more than one method. User authentication occurs
in the order the methods are selected. Possible methods are as follows:
• Local. The user’s locally stored ID and password are used for authentication. Since
the Local method does not time out, if you select this option as the first method, no
other method is tried, even if you specified more than one method.
• RADIUS. The user’s ID and password are authenticated using the RADIUS server. If
you select RADIUS or TACACS+ as the first method and an error occurs during the
authentication, the switch uses Method 2 to authenticate the user.
• TACACS+. The user’s ID and password are authenticated using the TACACS+
server. If you select RADIUS or TACACS+ as the first method and an error occurs
during the authentication, the switch attempts user authentication Method 2.
• None. The authentication method is unspecified. This option is available only for
Method 2 and Method 3.
8. From the menu in the 2 column, select the authentication method, if any, that must be used
second in the selected authentication login list.
This is the method that is used if the first method times out. If you select a method that
does not time out as the second method, the third method is not tried.
9. From the menu in the 3 column, select the authentication method, if any, that must be used
third in the selected authentication login list.
10. From the menu in the 4 column, select the method, if any, that must be used fourth in the
selected authentication login list.
This is the method that is used if all previous methods time out.
11. Click the Apply button.
The updated configuration is sent to the switch. Configuration changes take effect
immediately.










