SpeedTouchTM608WL and SpeedTouchTM620 only SpeedTouchTM608(WL)/620
Table Of Contents
- Contents
- About this IPSec Configuration Guide
- 1 IPSec: Concept for secure IP connections
- 2 SpeedTouch™ IPSec terminology
- 3 Configuration via Local Pages
- Prerequisites
- IPSec Web Pages
- VPN Menu
- In this section
- 3.1 LAN to LAN Application
- Reference network
- Selecting the LAN to LAN application
- Outline of a configuration procedure
- 3.1.1 Remote Gateway Address Known Page
- VPN context
- Initial page
- Buttons
- Remote Gateway
- Miscellaneous
- IKE Security Descriptors
- Page layout with additional Descriptors
- Page layout for pre- shared key authentication
- IKE Authentication with Preshared Key
- Page layout for certificate authentication
- IKE Authentication: Certificate parameters
- Example of a completed page
- Buttons
- 3.1.2 Remote Gateway Address Unknown Page
- VPN context
- Example
- Aggressive Mode initial page
- Aggressive Mode versus Main Mode
- Buttons
- Miscellaneous
- IKE Security Descriptors
- Page layout with additional Descriptors
- Page layout for pre- shared key authentication
- IKE Authentication with Preshared Key
- Page layout for certificate authentication
- IKE Authentication: Certificate parameters
- Main Mode initial page
- Buttons
- IKE Security Descriptors
- Page layout with additional Descriptors
- Miscellaneous
- Page layout for pre- shared key authentication
- IKE Authentication with Preshared Key
- Page layout for certificate authentication
- IKE Authentication: Certificate parameters
- Main mode expanded page
- Identification & Interface
- Example of a completed page
- Buttons
- 3.1.3 Connections Page
- 3.2 VPN Client
- VPN context
- Advantages of the SpeedTouch™ VPN Client
- Selecting the VPN Client application
- Outline of a VPN Client configuration procedure
- 3.2.1 VPN Client Page
- Initial page
- Buttons
- Server IP Address or FQDN
- Backup Server IP Address or FQDN
- IKE Security Descriptor
- IPSec Security Descriptor
- Exchange Mode
- Server Vendor
- Primary Untrusted Physical Interface
- Virtual IP mapping
- Optional Remote network
- Page layout for pre- shared key authentication
- IKE Authentication with Preshared Key
- Page layout for certificate authentication
- IKE Authentication: Certificate parameters
- Starting and stopping a VPN client connection
- Page layout for Automatic Start
- Local LAN IP Range
- Set of Server Vendor specific parameters
- Configuring XAuth
- 3.2.2 Starting the VPN Client Connection
- 3.2.3 Closing a Connection
- 3.3 VPN Server
- VPN context
- Selecting the VPN Server application
- Outline of a VPN server configuration procedure
- 3.3.1 VPN Server Page
- Initial page
- Buttons
- Local Trusted Network
- Page layout with additional Networks
- IKE Security Descriptor
- Page layout with additional Descriptors
- IPSec Security Descriptor
- Page layout with additional Descriptors
- Miscellaneous
- VPN Server settings
- Page layout for pre- shared key authentication
- IKE Authentication with Preshared Key
- Page layout for certificate authentication
- IKE Authentication: Certificate parameters
- Authorized Users List
- 3.4 Certificates
- 3.5 Advanced VPN Menu
- When to use
- Peer Profiles page
- Connection Profiles page
- 3.5.1 Peer Profiles Page
- 3.5.2 Authentication Page
- 3.5.3 Peer Descriptors Page
- 3.5.4 Peer Options Page
- 3.5.5 VPN-Client Page
- 3.5.6 VPN-Server Page
- 3.5.7 VPN-Server-XAuth Page
- 3.5.8 Connection Profiles Page
- 3.5.9 Networks Page
- 3.5.10 Connection Descriptors Page
- 3.5.11 Connection Options Page
- 3.5.12 Client Page
- 4 Configuration via the Command Line Interface
- In this chapter
- Reference network
- 4.1 Basic IPSec configuration procedure
- 4.2 Peer: Authentication Attribute
- 4.3 Peer Security Descriptor
- 4.4 Peer
- What is ...
- How is it used
- In this section
- 4.4.1 Peer parameters
- Parameters table
- Peer name [name]
- Remote Security Gateway identifier [remoteaddr]
- Backup remote Security Gateway Identifier [backupaddr]
- Exchange mode [exchmode]
- Local Identifier [localid]
- Remote Identifier [remoteid]
- Physical Interface [phyif]
- Peer descriptor [descr]
- Authentication Attribute [auth]
- client/server
- options
- 4.4.2 List all peer entities
- 4.4.3 Create a new peer entity
- 4.4.4 Set or modify the peer parameters
- 4.4.5 Delete a Peer entity
- 4.5 Connection Security Descriptor
- 4.6 Network Descriptor
- 4.7 Connection
- 4.8 Auxiliary Commands
- 4.9 Organisation of the IPSec Command Group
- 5 Troubleshooting SpeedTouch™ IPSec
- 6 Advanced Features
- In this section
- 6.1 IPSec and the Stateful Inspection Firewall
- 6.2 Surfing through the VPN tunnel
- 6.3 Extended Authentication (XAuth)
- 6.4 VPN Client
- 6.5 VPN Server
- 6.6 XAuth Users Pool
- Introduction
- 6.6.1 XAuth Pool parameters
- 6.6.2 Create a new XAuth pool
- 6.6.3 Modify the xauthpool type
- 6.6.4 Attach the xauthpool entity to the vpnserver entity
- 6.6.5 Delete an xauthpool entity
- 6.6.6 XAuth User parameters
- 6.6.7 Create a new XAuth user
- 6.6.8 Set or modify the password of an XAuth user
- 6.6.9 Delete an xauthuser entity
- 6.7 The Default Peer Concept
- 6.8 One Peer - Multiple Connections
- 6.9 Peer Options
- 6.10 Connection Options
- 6.11 Advanced Connection
- Need more help?
Chapter 3
Configuration via Local Pages
E-DOC-CTC-20051017-0169 v0.1
83
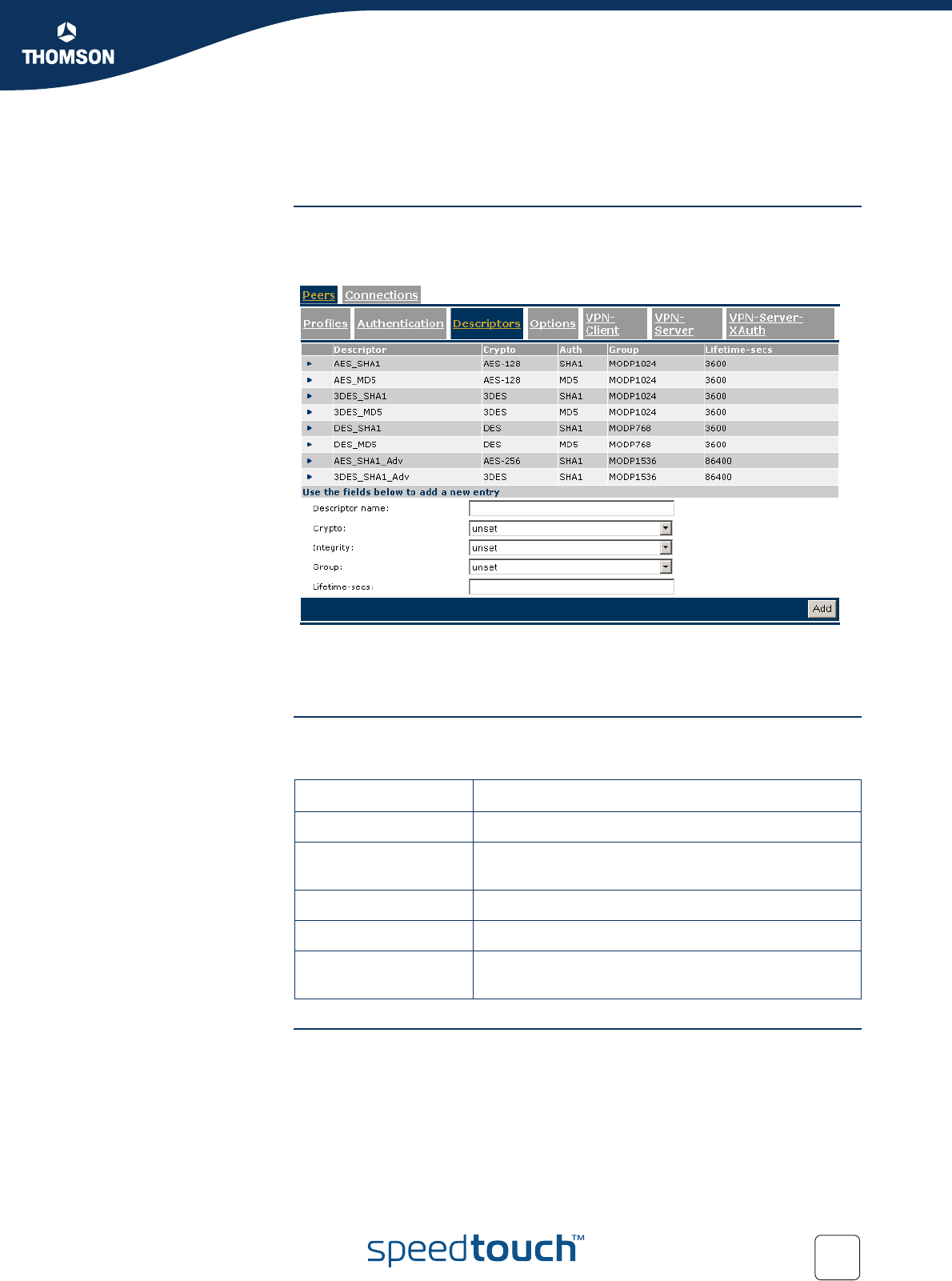
3.5.3 Peer Descriptors Page
Descriptors
page layout
A Peer Security Descriptor contains the methods for message authentication,
encryption and hashing, and the lifetime of the IKE Security Association.
The Peer Descriptors page allows you to manage Peer Security Descriptors.
A number of Peer Security Descriptors are pre-configured in the SpeedTouch™.
You can verify and modify the contents of the pre-defined Security Descriptors or
define your own Security Descriptors.
Parameter table The following table summarizes the parameters comprised in the peer security
descriptor:
Peer Descriptor name This name is used internally to identify the Peer Security Descriptor. This name
appears in the Descriptor lists on the Peer Profiles page.
Parameter Description
Descriptor name Symbolic name to identify the Descriptor.
Crypto
Cryptographic function used for encrypting the IKE
messages.
Integrity Hashing function used for message authentication
Group Diffie-Hellman group for key exchange
Lifetime-secs
The lifetime of the IKE Security Association. At
expiration of this period re-keying occurs.










